When I got my first bank card back in 2010, I got really interested on how these small magnetic stripe cards (or Magstripes for short) worked. In Venezuela, getting your card cloned or simply stolen (via muggings) was (still is) extremely common. This problem peaked my interest and I wondered how easy it would be to say, clone my own debit card and dump it into a Blockbuster card (or any other rewards card). That way, if I ever got mugged, the robbers would leave my back account alone.
While I knew this was possible, and I had a lot of curiosity, finding the tools in Venezuela wasn't as simple or cheap as I expected. Seeing these complications, I decided to shelf the idea and instead focus on something else (like my encryption protocol: CasualKrypt).
Fast-foward to 2012; Having recently moved to the US, I walked into a store and was surprised to see the cashier was using an Ipad with a dinky piece of plastic called a square card. I immediately unshelved my dream of magstripe hacking and ran back home to buy a couple of square cards. While doing my research, I was amazed to find how much information had suddenly appeared on the topic of magstripes between 2010 and 2012. (or perhaps I had just gotten better at googling things.) Even wikipedia had a fantastic description of the encoding used in magstripes.
Quickly enough I understood the basics behind magstripes. Let's take a very brief overview:
The black strip behind any magstripe card is divided into small segments. Each of those segments are magnetized in such a way that represent 1's and 0's.
Cue physics; when a magnet is moved near a copper wire, it will induce current in this wire. So in theory, all you really need for a simple reader would just be a copper wire circuit and some way to measure it's current changes internally. The square card reader is simply a sensitive magnetic reader connected to the headphone jack. So you can theoretically plug a square card into your phone, turn on the audio recorder, swipe a card, and then open this recording in an audio editing program and you would see the digital output presented above.
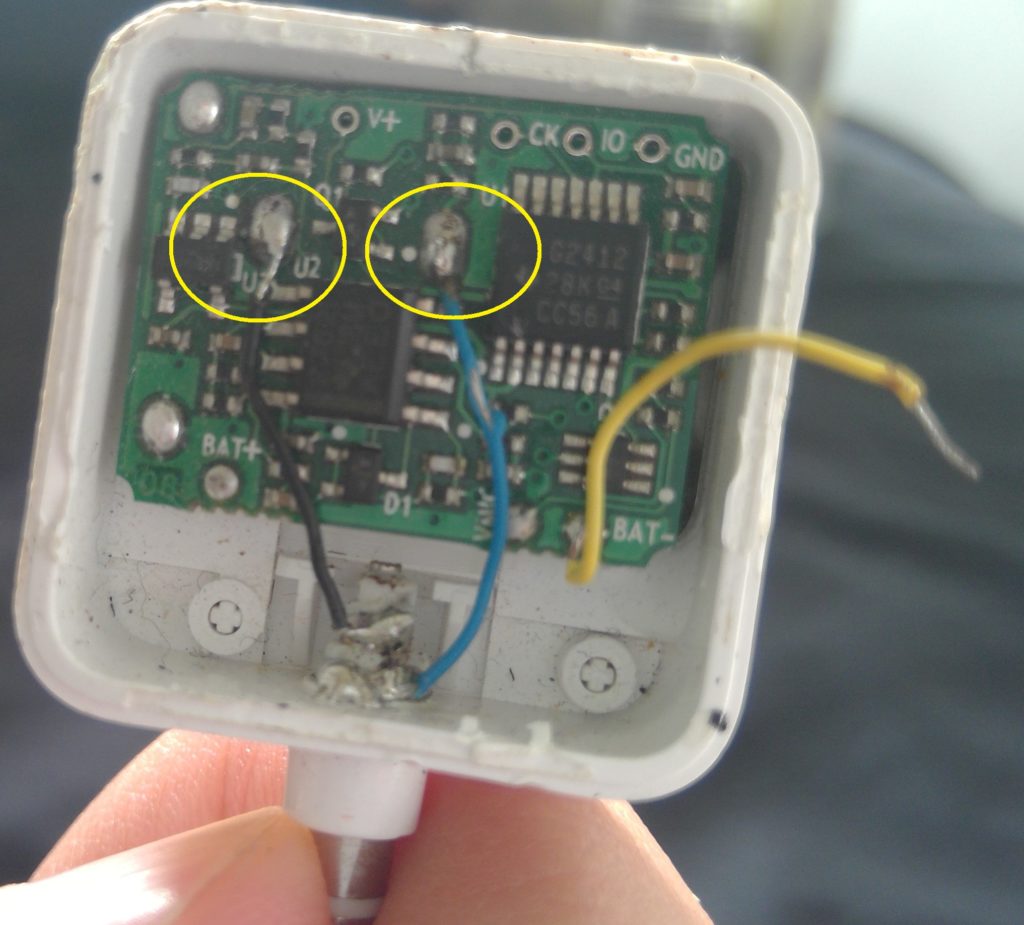
So when my square cards finally arrived, I swiped a couple of cards and decided to view them in Audacity (Audio manipulation program). However, instead of seeing the rectangular waves of 1's and 0's. I saw this weird curvy wave without any uniform spacing. I tried googling my situation, and somewhere along the line, I found a picture of an opened square card. In it, there was a simple magnetic reader connected to the audio jack. I decided to open mine and see if anything was broken, Instead I found a chip inside. What?!


It turns out that circa 2011, people had realized that people could read credit cards with them. For some reason, this freaked people out and they were forced into adding encryption on their device. Of course, this was just a wet wipe, because the fact is that if you really really cared about security, a more proper solution was to start using chips *(like Europe and even Venezuela did by then). Anyhow, I don't consider myself a hardware guy, but I decided to see what would happen if say...I bypassed the chip and simply connect the magnetic reader to the output jack. Since the reader itself is attached to the chip, I had to tinker a little bit to find where exactly it was connected. Since they were a buck per square card, I just completely butchered one until I found the actual sodering points. After a few minutes of googling how to solder and which wire is supposed to be positive or negative, I finished modifying the reader.
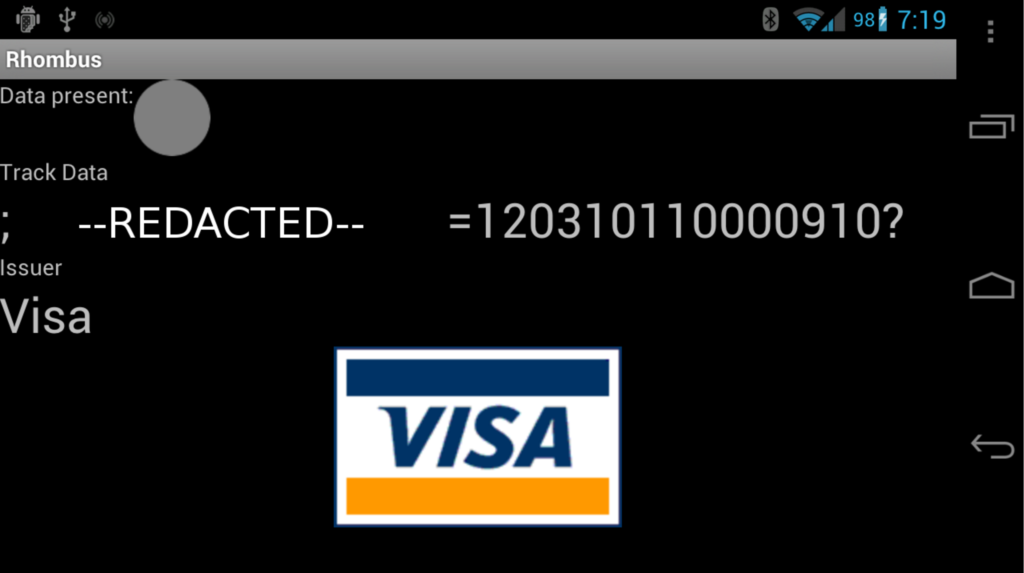
I crossed my fingers and tried again. Sure enough, the unencrypted data was there. At this point, I found an Android app called Rhombus which would read in the data and decode it to human readable form. This was a nice touch!
Fast-Foward to 2016; Companies in the US have finally "decided" (aka. waited until the last possible minute) to add chips to their magstripe cards! At the same time, magstripe reader/writers have dropped prices -- perhaps because we feel more secure now?
If you wanted to continue messing around with it, you could get a simple MSR 605X. Now, cloning a card with this beast is as simple as clicking two buttons, so that part doesn't really intrigue me as much (since there is no challenge and I am not one to go about stealing from people). However what is rather interesting to me, is understanding how people are using this magstripe medium. In other words, if an apartment complex uses magstripes for their doors, are they actually using a complicated encryption scheme such that I if someone had one apartment's card, could they deduce the other apartment's card info. Thus, if someone stole my neighbor's card, could they build a card that opened my door too?
Even within the world of financial security, many vulnerabilities are still abundant. Special today in the US, as many business still transition from magstripe to chip & pin. Stay tuned for an upcoming post were we dive deeper into these vulnerabilities.
Recent Comments