 pedro@konukoii:~$
pedro@konukoii:~$
Adventure
Generalist.
hacker · pilot · mountaineer · tinkerer · nomad · creative
 pedro@konukoii:~$
pedro@konukoii:~$
hacker · pilot · mountaineer · tinkerer · nomad · creative
Helping organizations understand their true security posture — before adversaries do. Works with Fortune 500s and organizations in highly regulated industries, spanning the full arc from traditional assessments to emerging disciplines like continuous red teaming and AI agent security.
Increasingly lives at the intersection of AI and security: studying how intelligent systems break, and building the tools that keep teams ahead of a threat landscape that keeps moving.
CNN-LSTM Hybrid Model ↗ 113 Citations PQC-AKE ↗ UCSB Thesis Full Works — Google Scholar ↗
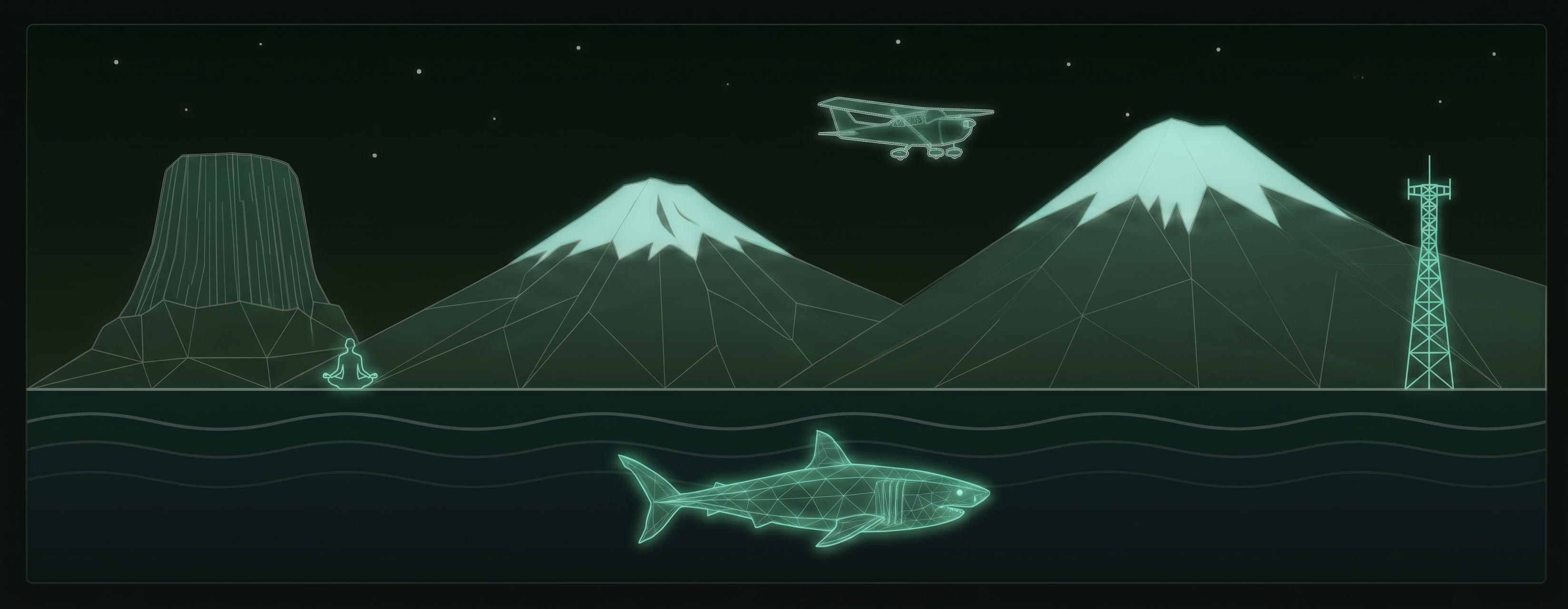
DuckHunt ↗ HID Defense Guardia ↗ Security Scanning Tripwire ↗ ESP32 · IoT
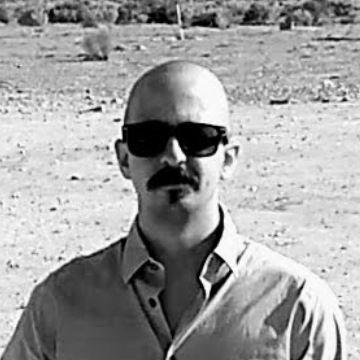
Jack of all trades. Licensed in most of them.
Private Pilot (PPL)Cessna-172 Wing-WalkingUS & UK Skydiving & Bungee13× Combined
Mt. Rainier14,411 ft Mt. Shasta14,179 ft Devils Tower5,112 ft
Scuba DiverAdvanced OW Cageless Shark DiverBullsharks Enriched AirNitrox
RYT-200 Yoga TeacherVinyasa Ham RadioGeneral License Dirt BikerYamaha TT-R230
Writing, visual art, music, and games — the parts of the work that live outside any terminal.
A running log since I first picked up a "Videogame Programming for Teens" book in 2006. Some things shipped, some things got cited in papers, one earned a Masters. More on GitHub ↗

Interpretive Phenomenological Analysis tool aimed at Psychology researchers. Built so researchers can focus on research, not tooling.

Multi-layer security scanning for packages, repos, and local code.

Helps students transcribe recorded webinars and classes, then ask questions about the material. Office hours that never close.
Smart door monitoring system using ESP32-WROOM-32E that detects door events and authenticates them via Bluetooth. Sends notifications showing whether activity was authorized or unauthorized.


Prevent RubberDucky and other keystroke injection attacks. Made the rounds on Hackaday and several cybersec outlets.
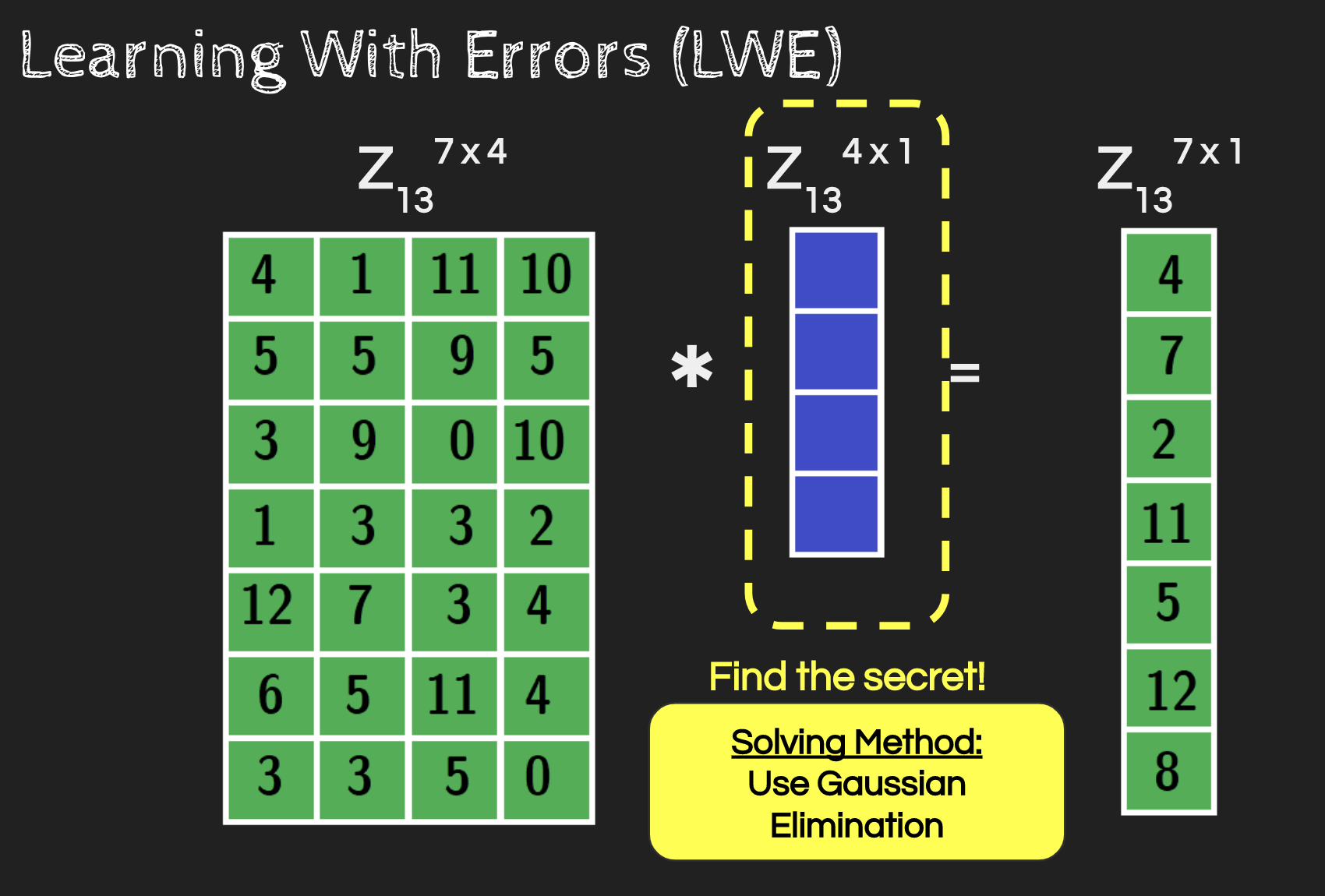
C++ implementation of a Post-Quantum Lattice-Based Authenticated Key Exchange protocol, based on Del Pino, Lyubashevsky & Pointcheval. This work earned the Masters.
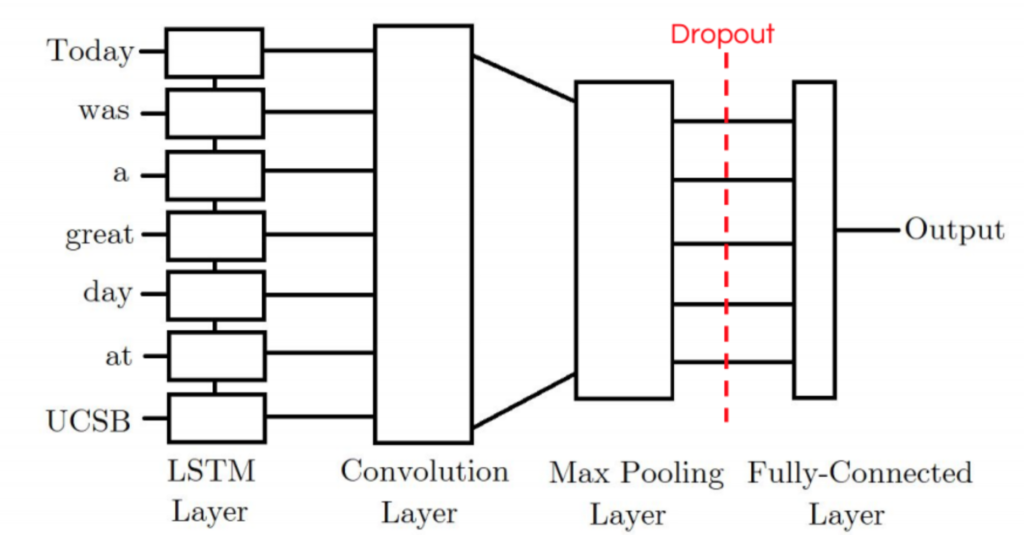
Combined CNN-LSTM neural network models for Twitter sentiment analysis, achieving 2.7–8.5% better performance over standard approaches. 110+ citations as of Q1 2026.
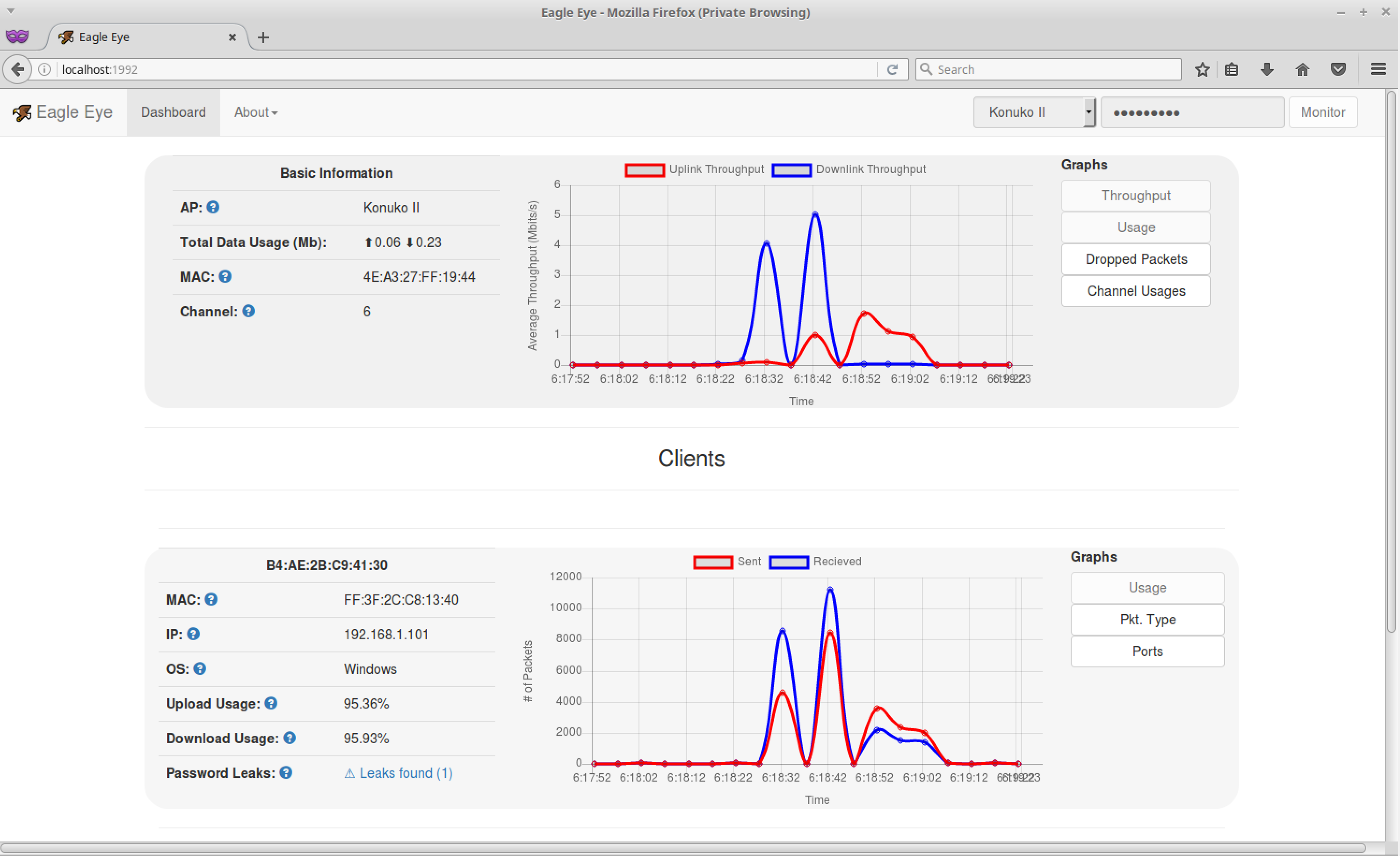
Wireless management software aimed at allowing non-technical sysadmins to understand how their networks are being used.
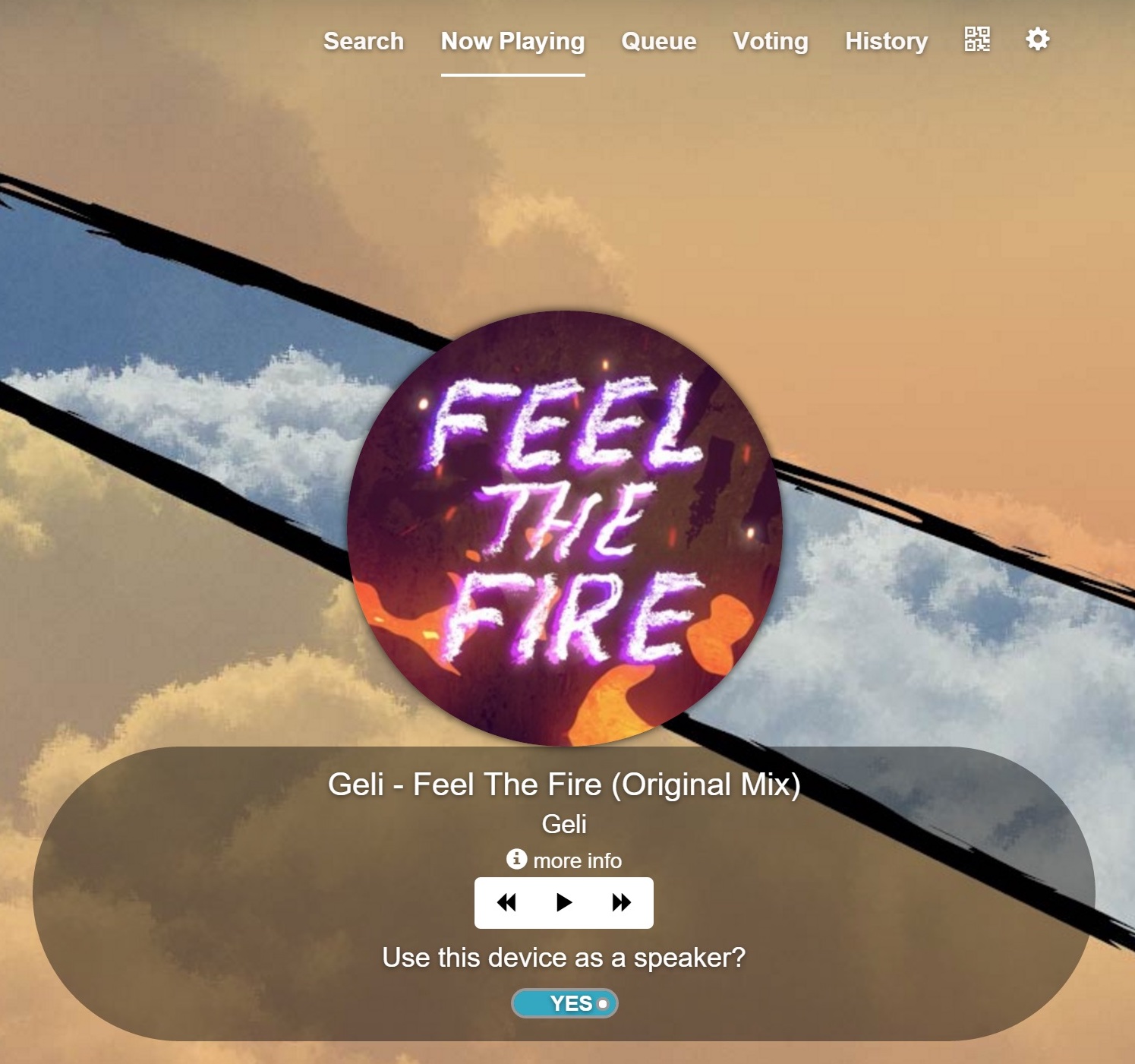
Collaborative music listening platform for partygoers and hosts to build playlists in real-time. Multi-speaker sync and AutoDJ. Won 3rd Place at UCSB Capstone.
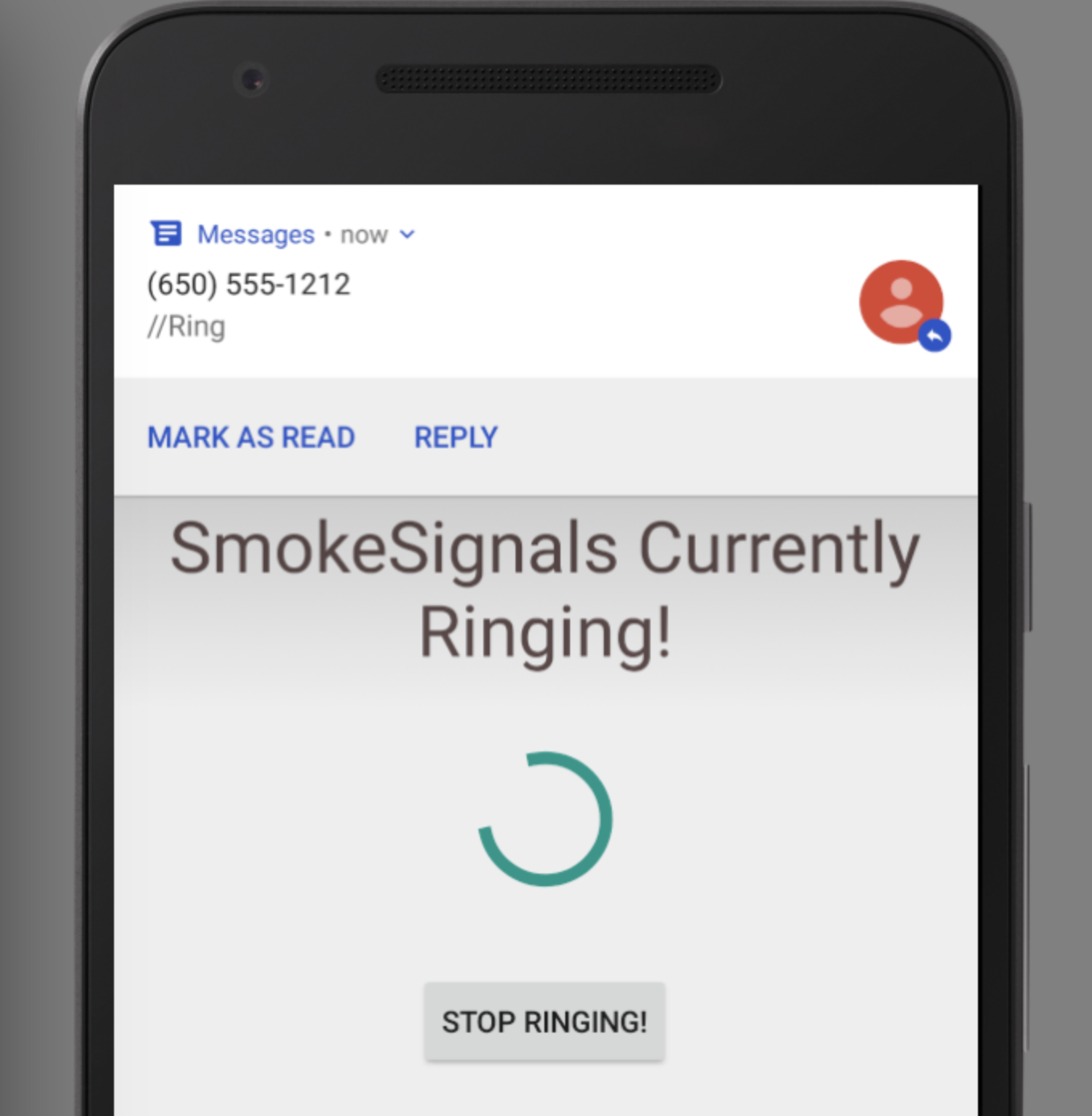
Android app that automates tasks triggered via incoming SMS. Still used by UCSB's CS56 Java class to teach Android development.

Website helping Venezuelans locate food & supplies during severe shortages, via social media scraping and crowdsourcing. My first site.
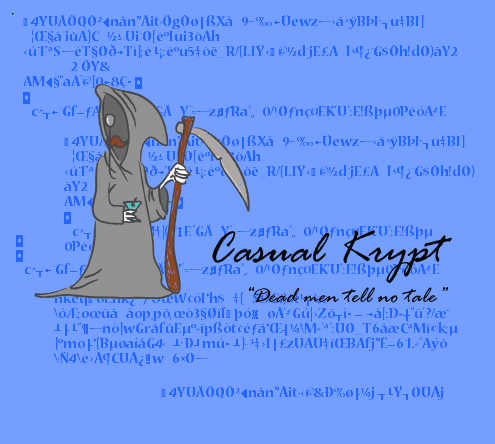
First experiment with cryptography: a (probably very unsafe) block cipher protocol with both C++ and Python cross-platform GUI and CLI apps.

After an art teacher said "you couldn't possibly build an arcade machine," spent a half year building a fully functional one with 5 original games. Later presented at an art gallery.

First program, coded at 15 in Blitz Basic. Went on to be used internationally in multiple Model United Nations conferences. Not the prettiest code, but the nostalgia is real.

It all started with a "Videogame Programming for Teens" book, some rough sprites made in MS Paint, and a few lines of Blitz Basic code.
Interesting problems, collaborations, and conversations about security, aviation, mountains — or all three at once.
konukoii@gmail.com// may be mid-climb; will respond when back in range